getNEXT is an IT consulting company, empowering businesses to maximise the impact of technology, content and communications.
Solutions for maximising productivity to simplify and facilitate collaboration.
State-of-the-art security and Cloud transformation.

getNEXT offers a range of Salesforce products aiming at providing a scalable and personalised CRM experience.




getNEXT networking products make it easier to set and manage networks while improving their security. getNEXT simplifies cost efficiencies and improves the performance of a business' network for greater, business-wide agility and responsiveness.


getNEXT's Publishing solution provides businesses with a secure, Cloud-based platform that allows content to be created once and published everywhere.

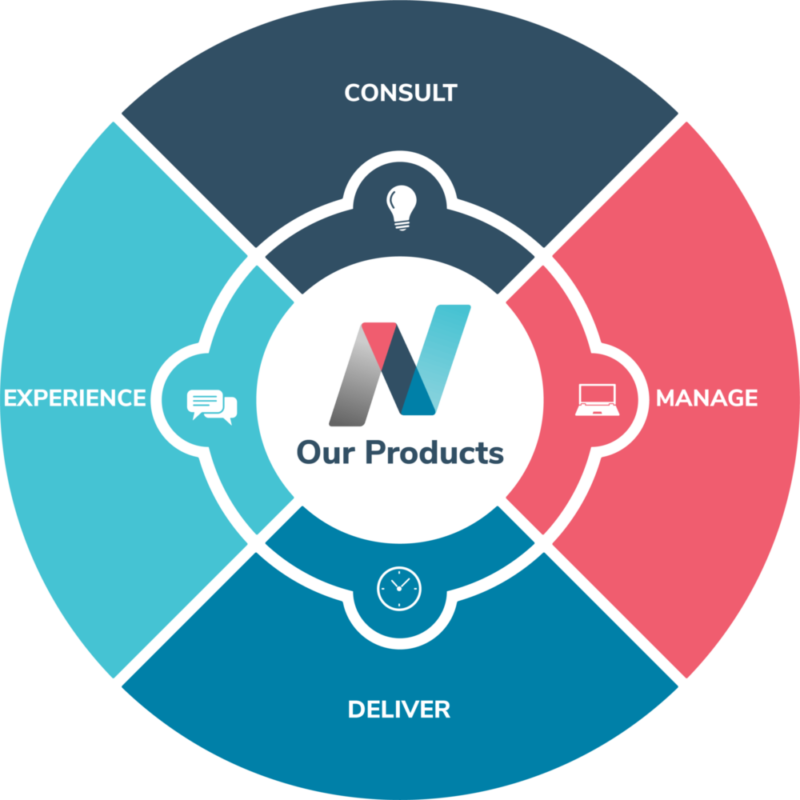
CONSULT
getNEXT enables companies to achieve productivity gains through Cloud healthchecks, audits and consulting products that align to a business’ needs.
getNEXT offers a range of products aiming at providing a scalable and personalised experience.


MANAGE
getNEXT’s Cloud solutions provide next-generation environments, creating cost-effective business solutions. Our range of Cloud products cover everything from data backup to Cloud migrations, including productivity apps and managed IT services.
DELIVER
getNEXT’s security offering includes a series of cyber security tools aimed at preventing data loss and network vulnerabilities, ensuring a business’ ability to recover safely and quickly from a cyber-attack or disaster.
getNEXT networking products make it easier to set and manage networks while improving their security. getNEXT simplifies cost efficiencies and improves the performance of a business’ network for greater, business-wide agility and responsiveness.


EXPERIENCE
getNEXT makes the MarTech ecosystem smart. getNEXT’s Marketing Enablement solution doesn’t want to replace the entire technology stack, it makes it work better – supercharging a business’ workflows, fueling amazing content, streamlining delivery and creating true closed-loop reporting.
getNEXT’s Publishing solution provides businesses with a secure, Cloud-based platform that allows content to be created once and published everywhere.